Monitoring Cisco IPSec VPN Tunnels with Nectus
Monitoring Cisco IPSec VPN Tunnels with Nectus
One of the key features introduced in Nectus 1.2.51 is ability to automatically discover and monitor Cisco IPSec VPN Tunnels terminated on ASA Firewalls and regular IOS routers.
- Tunnel Discovery
As part of regular scheduled network discovery Nectus attempts to detect existing VPN tunnels on all routers and firewalls by polling standard SNMP MIB: CISCO-IPSEC-FLOW-MONITOR-MIB
reserved for VPN Tunnels.
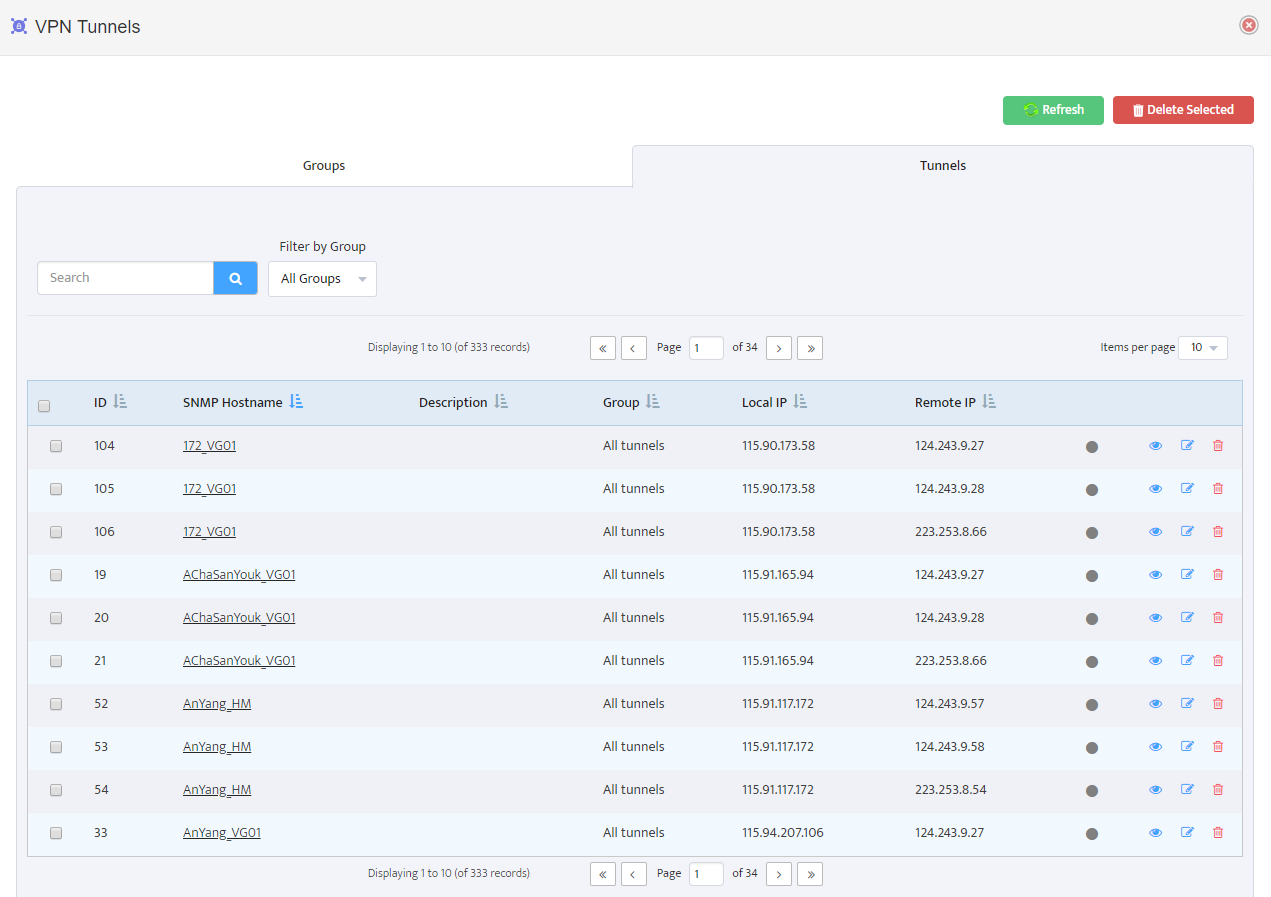
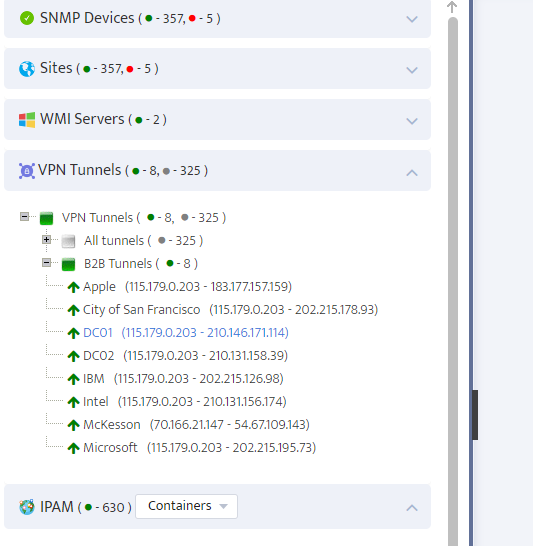
All discovered VPN tunnels can be seen in Main menu: Inventory → VPN Tunnels
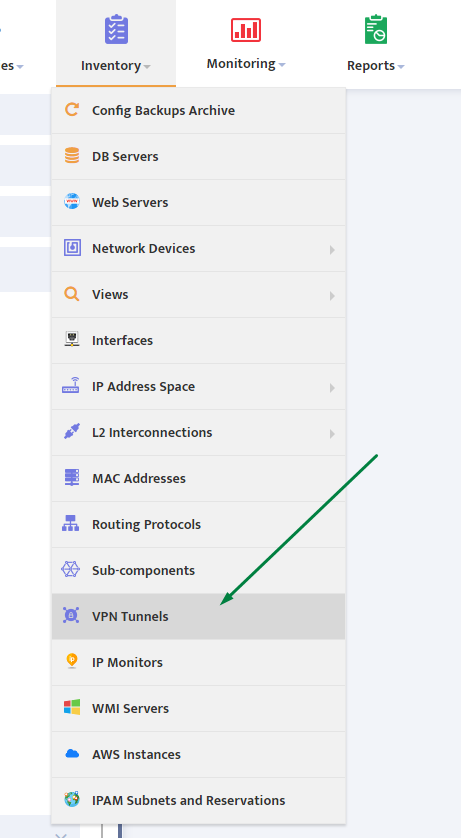
All discovered tunnels displayed as a table with Terminating Device, Group, Local and Remote IP Address visible in individual columns.
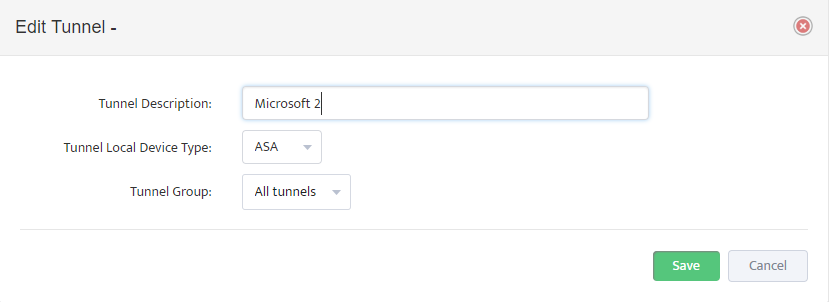
You can assign a human friendly name to each tunnel by pressing Tunnel Edit button on the right.
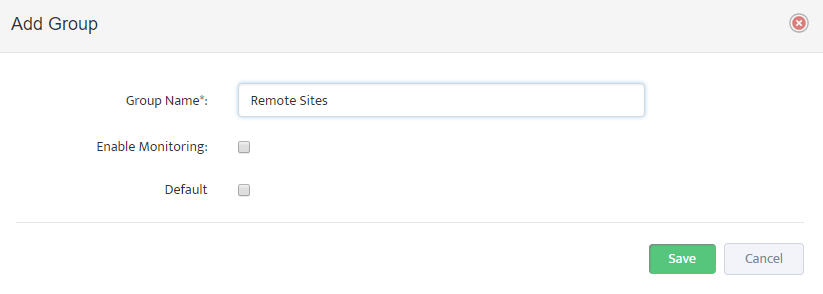
- Creating Groups and Assigning Tunnels to Groups
Each Tunnel must be assigned to an individual group with newly discovered Tunnels being automatically assigned to a group with “Default” parameter set to On.
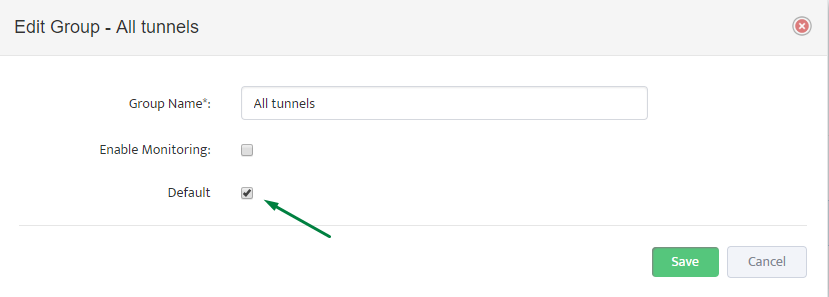
User can create multiple different groups and group tunnels in any way that is appropriate.
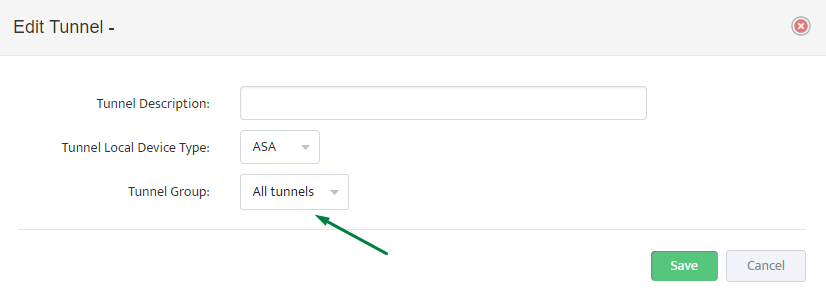
User can change Tunnel-to-Group assignment by using context menu or by using “Edit VPN Tunnel” button.
- Enabling Tunnel Monitoring
Once all Tunnels are discovered and added to a correct group you can enable monitoring on group level by setting “Enable Monitoring” check-button to “ON”
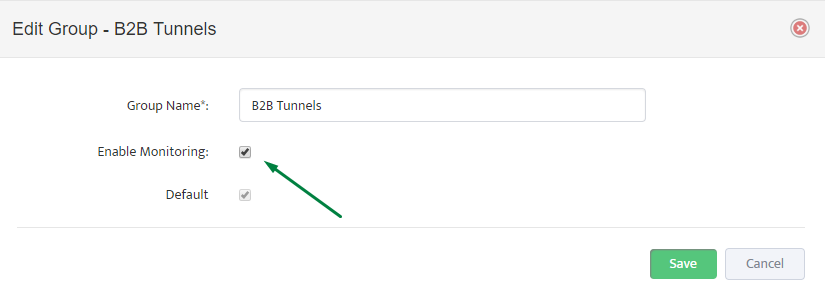
After “Enable Monitoring” flag is set to ON, Nectus starts checking Tunnel’s status every 5 min and creating records in Alert log along with sending Alert emails in case if Tunnel is down.
Real Time status for all tunnels can be seen in left side panel “VPN Tunnel”
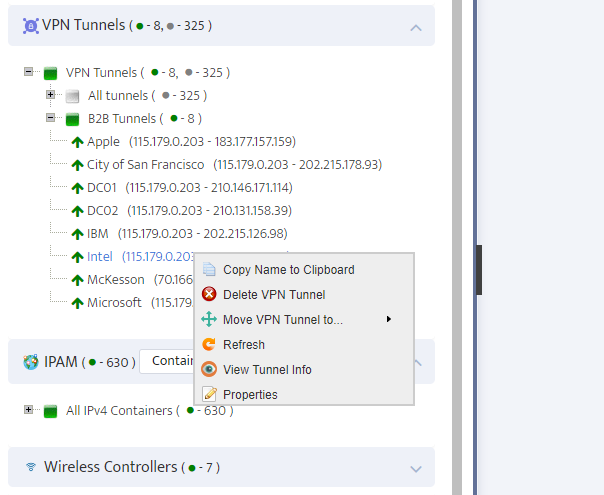
By using right-click on Tunnel’s name you can access rich context menu where you can move tunnels to a different group, delete Tunnel, change Tunnel’s name or
View Tunnel’s Phase 1 and Phase 2 Information.
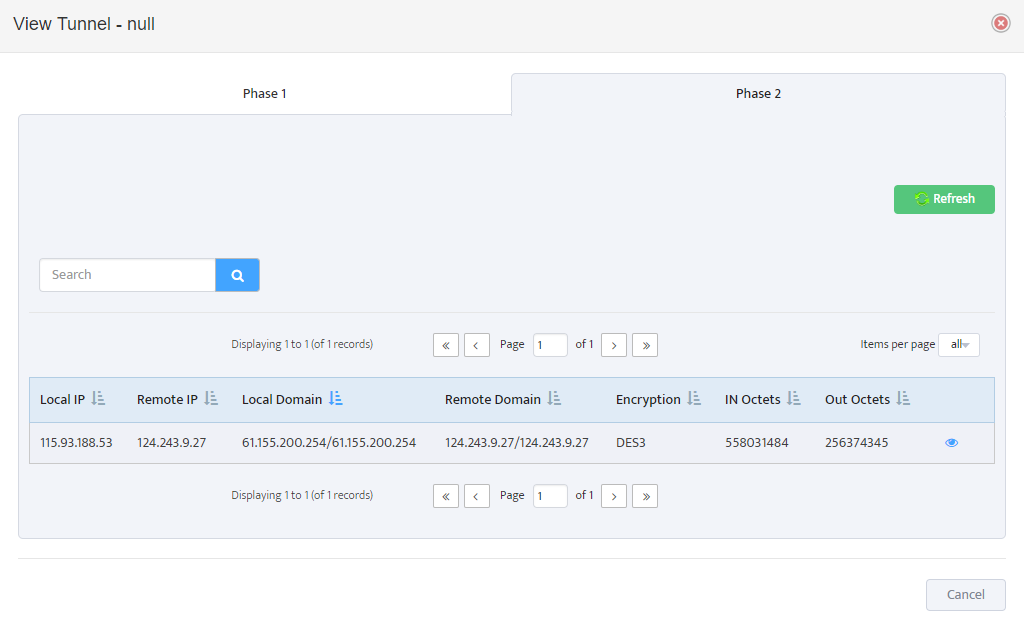
“View Tunnel Info” provides low level Phase 1
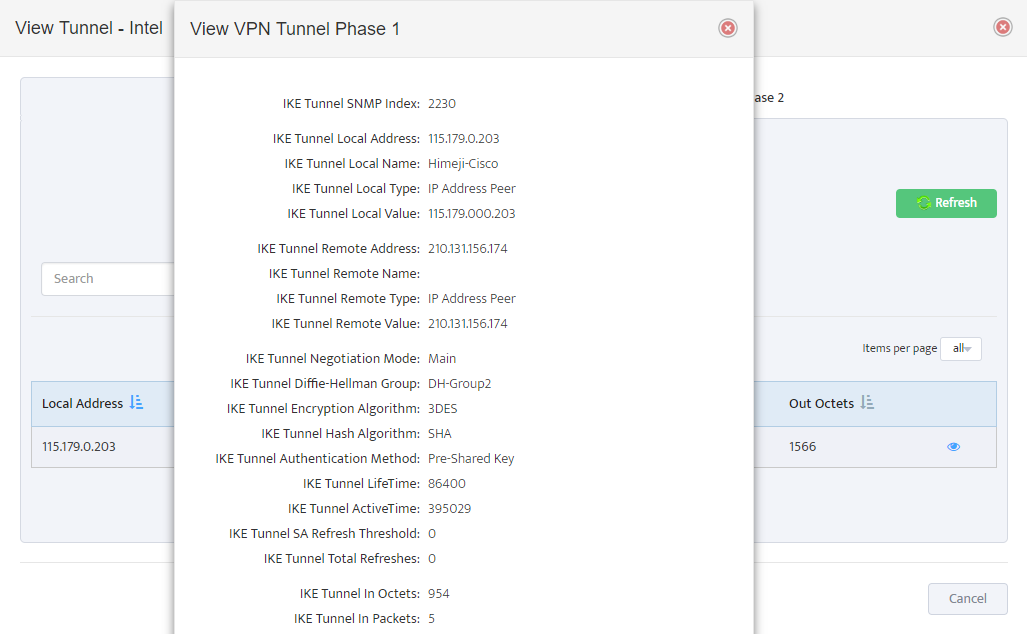
And Phase 2 Information along with encryption domain parameters and traffic counters